Change the Synology Default SSH Port
The Synology has a nice option to block IP addresses with more than 5 failed login attempts. This is really just swatting at flies most of the time. It’s a better idea to change the SSH port.1
Login as root, not as admin. This will require an SSH session like this:
:::shell
ssh root@your.NAS.ip.address
Root uses the same password as the admin account.
Next, edit two configuration files
:::shell
DiskStation> vi /etc/ssh/sshd_config
DiskStation> vi /etc.defaults/ssh/sshd_config
In both cases uncomment the line #Port 22 and change the port number to something that will not conflict. The forum user recommends port 10022 but I’ve seen many connection attempts at similar ports that end with 22.2
Now if someone attempts an SSH connection on the Synology it will simply display connect to host XXX.XXX.X.X port 22: Connection refused
If you need to SSH back into the NAS, use this now:
:::shell
ssh -p 10022 root@XXX.XXX.X.X
DSM updates have a nasty habit of resetting the sshd_config file so plan to do this over again whenever there’s a new update.
I also strongly recommend enabling the 2-Factor authentication for the Synology.
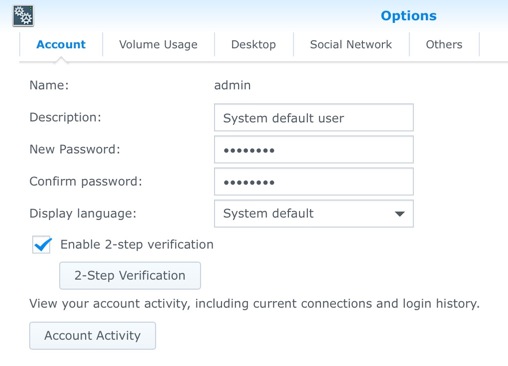
It’s a mild pain to login because you will need the Google Authenticator app on iOS available. But if you lose your phone you can always reset the NAS.
-
Don’t be a dummy. If you don’t understand any of this stuff, then don’t mess with it and remove external access to your NAS instead. Or educate yourself a little first. You can totally bork your expensive hardware messing with these files. ↩︎
-
It’s debatable if changing the port number is effective at all. I can tell you my connection attempts dropped from 12-30 a day to zero when I changed the port. Kind of like a door lock. It keeps minimally skilled scumbags out. ↩︎